Welcome
#Welcome to the Tech News section of FroJoe.Pro.
This area of the site is being developed as a practical resource for everyday technology users — a place to stay informed about scams and fraud threats that continue to target individuals, families, and small businesses, as well as to explore emerging technologies and tools that may affect how we work and live.
As this section grows, you can expect straightforward discussions on:
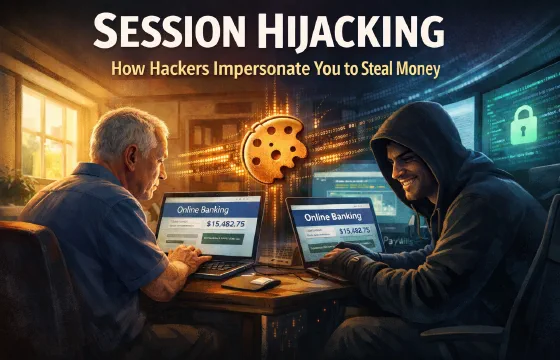
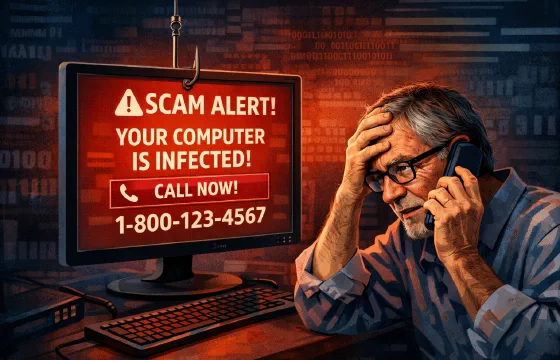
- Current scam trends and real-world warning signs
- Fraud prevention and digital safety practices
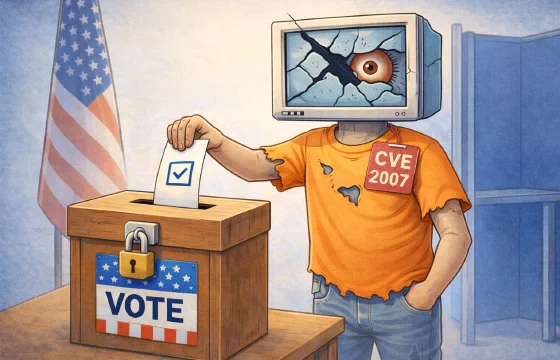
- New and evolving technologies worth understanding
- Practical insights into how Joe and Kayla’s services can support secure and reliable technology use
The goal here is simple: provide useful, grounded information that helps people make better decisions with the systems they rely on every day.
More content will be added soon.