
Today I want to talk about a security threat known as “browser session hijacking.”
This is an attack where a hacker steals the information that identifies you on the internet. Once successful, the attacker has unchallenged access to your online banking, social media, and other online accounts — without ever needing your password. The scary part? You’d never know it was happening.
As you browse the internet, you’re likely logging into services like online banking, social media, wealth management, and email — just to name a few. Have you noticed that you tend to stay logged in even after stepping away from your computer for a bit? That’s your session at work — it persists for a set window of time so you don’t have to re-authenticate every few minutes.
Have you ever wondered how that session keeps itself alive — and what could go wrong if someone else got hold of it? That’s exactly what we’re going to unpack today, in plain terms.
Web Browser Sessions#
So there you are, logging into www.YourBank.com. You’ve been reading FroJoe’s Tech Insights, so you already know to verify that web address every single time you access it. But what’s actually happening behind the scenes?
When you land on the login page, you enter your username, password, and the 6-digit code that just arrived on your phone. Login successful — and at that moment, your browser and the bank’s server have initiated the creation of a session. The bank generates a session ID, a temporary “key” or “cookie,” and sends it to your browser. Think of it as a private, time-limited handshake code that tells the bank: this is the authorized user who just logged in, and we can trust them for now.
This session ID is what keeps you logged in as you navigate between pages. That detail matters — a lot.
Session Hijacking#
Now that you’ve established a session with your bank, you step away for a few minutes to grab a document. The page is still loaded, you’re still logged in, and your session is still active. Take too long, though, and you’ll come back to a login screen — the session timed out.
Here’s the problem: a hacker who captures your session ID doesn’t have to wait for it to time out. They can keep that session alive on their own system, staying logged in until they decide to make their move. At that point, they have full access to your account — without ever knowing your password.
So how do they get your session ID in the first place?
There are a few ways a hacker can steal your session information:
- Malware
- Listening in on Wi-Fi / network traffic
- Intercepting your session information with packet listeners
- Malicious website code execution
- Guessing (less common, but it happens)
The most common method is malware. Even if you didn’t intentionally download anything, you can still be infected through what’s known as a “drive-by download” — malicious code that runs just from visiting a compromised page. Once executed, it bundles up your session IDs and sends them off to the attacker.
Intervention: Web Content Filtering
We block known and suspected malware links before they reach you
Intervention: Active Threat Monitoring
Our 24/7 Security Operations Center is always watching
Eavesdropping#
Hackers don’t always need to compromise your machine directly. Sometimes they simply listen.
Network eavesdropping — capturing data as it moves between your device and the internet — is a well-established attack method. Public Wi-Fi is the classic concern: an attacker on the same open network can position themselves to intercept traffic. Today, most websites use HTTPS encryption, which makes directly lifting usable session data much harder — but not impossible. Attackers have shifted to targeting the weak points around encryption: unsecured connections, misconfigured sites, or fake Wi-Fi networks that look legitimate enough to fool you into connecting.
There’s another angle that often gets overlooked — your own home or office network. Smart TVs, cameras, thermostats, printers, and other “Internet of Things” devices are frequently under-secured and rarely updated. Once one of those devices is compromised, an attacker can use it as a quiet foothold inside your network to monitor traffic or probe for other targets.
This risk is amplified significantly for anyone who works or manages finances on the road. Marina Wi-Fi, RV park networks, hotel lobbies, coffee shops — these are shared, largely unmanaged networks where you have no idea who else is connected or what they’re running. For full-time travelers and remote professionals, this isn’t an occasional risk. It’s the daily reality.
It’s also worth knowing that attackers don’t always use what they steal. In many cases, captured session data and credentials are packaged up and sold through underground marketplaces. Your information can pass through multiple sets of hands before it’s ever actually used against you.
Intervention: Active Network Monitoring and Management
Our Defend Package includes monitoring and management of a dedicated hardware security device
Exploitation of Vulnerabilities#
Vulnerabilities in your browser, operating system, or other applications can give a hacker a direct path to your session IDs and cookies. New vulnerabilities are discovered every day, and malware is written specifically to exploit them. This malware can interact with your browser to extract session data and send it to the attacker — and it doesn’t even have to live on your computer to do it. It can be injected into a website — yes, even legitimate ones, through a compromised ad or a hacked page — and perform what’s called “remote code execution.” That means a hacker can instruct your computer to do things remotely: send them your session IDs, harvest other useful data, or quietly establish a persistent foothold. This is exactly why behavioral detection — the kind built into our MDR service — is so important. It’s not a catch-all, but it’s the most effective tool we have against threats that haven’t been documented yet. Once a threat is identified and documented by the security community, it gets assigned a CVE — a Common Vulnerabilities and Exposures number.
Take a look at the image to the right (or below on smaller screens). That’s a screenshot from an RSS feed I subscribe to, pulling in cybersecurity news from various vendors. This particular feed tracks intelligence from the Microsoft Security Response Center. They identified and numbered approximately 32 previously undiscovered vulnerabilities in the Chromium browser engine — the system that powers Google Chrome, Microsoft Edge, and dozens of other browsers. That’s a lot of new attack surface, discovered in even a single disclosure.

Intervention: Patch Management
FroJoe actively manages updates for your computers and supported software to keep you protected.
Patch management is a core component of our Managed Service Plans. We handle operating system updates and supported application updates so your systems are always running the latest security fixes — including antivirus definition updates that allow detection of newly documented malware.
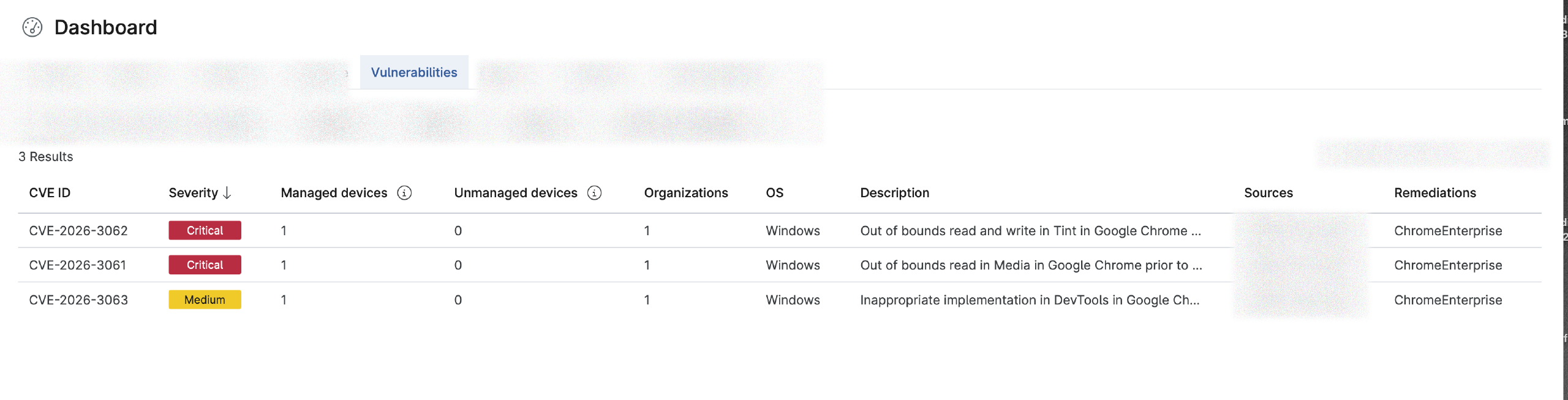
Take a look at the screenshots below — you may want to tap or click to enlarge them. The first is from our vulnerability monitoring system, where we track CVEs across every computer we manage. Chromium shows up again here, this time with a different CVE number. This is completely normal — vulnerabilities are discovered constantly by ethical researchers, development teams, and sometimes by catching an attacker in the act. A rapid, consistent patching cycle is one of the most effective defenses available.
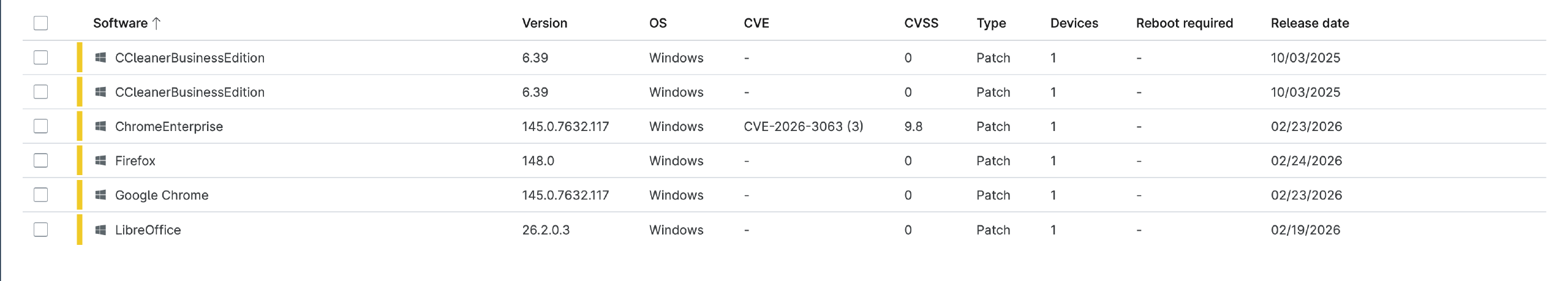
The second screenshot is from our patch management system. You’ll notice the same CVE number from above appears here with a corresponding patch ready to deploy — we have a solution for the identified problem. Also note the dates on the right side of the screen. Some of the entries show “CCleaner Business Edition” sitting four months out of date. These updates were for a newly onboarded client, and we were still catching up on deferred patches when these CVE notices came through. That’s exactly the kind of gap our service is designed to close.
How FroJoe Helps#
The goal at FroJoe Tech Services is simple: reduce your risk before problems find you. That means tracking security advisories, applying patches as vulnerabilities are disclosed, and monitoring your systems for signs of suspicious activity — consistently, not just when something goes wrong. By addressing both documented vulnerabilities and unusual behavior in real time, we work to close the most common attack paths before they’re ever exploited.
For home users and small businesses who don’t have the time or bandwidth to follow every security bulletin, managed support is a practical, cost-effective way to keep your technology maintained, monitored, and working for you — not against you.
Want Help Protecting Your Computer?#
If you’re a home user, small business, or someone who manages your finances and work remotely — whether that’s from a home office, a marina, or an RV park across the country — you don’t have an IT department watching your back. That’s exactly who FroJoe Tech Services is built for.
We offer proactive monitoring, security hardening, and remote technical support that works wherever you are. No office visit required.
Reach out anytime — we’ll take an honest look at where you stand and what actually makes sense for your situation. No pressure, no jargon.
