Tech Support Scams — What They Look Like and How to Shut Them Down#
Since you are reading this I will assume that you’ve probably seen one of these:
A browser window suddenly claims your machine is infected with a virus or possessed by a hacker.
A phone call claiming to be from “Microsoft Support” or another recognizable company.
An email says you’ve been charged for something you didn’t buy and to call immediately to be refunded or cancel the order.
These are tech support scams — and they’re still one of the most common fraud tactics in circulation. They don’t rely on sophisticated hacking. They rely on panic, urgency, and social engineering.
According to the FBI and the FTC, scammers use these methods because they consistently lead victims to grant remote access or make payments under pressure.
If You Read Nothing Else, Read This:#
- Scammers reach out — or manipulate situations so you reach out to them.
- They ask for payment methods that are difficult or impossible to reverse: gift cards, crypto, wires, or mailed cash/cards.
- They create urgency to keep you from pausing to verify.
If something feels off, stop. Do not pay.
If you absolutely must transact and aren’t fully certain, use a credit card — it provides the strongest dispute protections available to consumers.
Scammers will do everything they can to keep you from seeking the advice of others.
They may become hostile, urgent, or threatening to isolate you.
That’s a warning sign — pause and get a “gut check” from someone you trust.
How the Scam Usually Works#
Most of these follow the same pattern.
1. The Alarm#
Something triggers fear:
- A pop-up warning that won’t close
- A phone call claiming your system is compromised
- An email about suspicious charges or expiring protection
- A text message claiming to be a known company offering to help with an urgent matter
Consider the below screen-shots. These appeared on my phone after I clicked a link on a post that a friend was tagged in. This was one of those “How horrific he will be missed by all after a horrible car accident” posts. I knew that this was a scam link and wanted to gather some image media for this post.
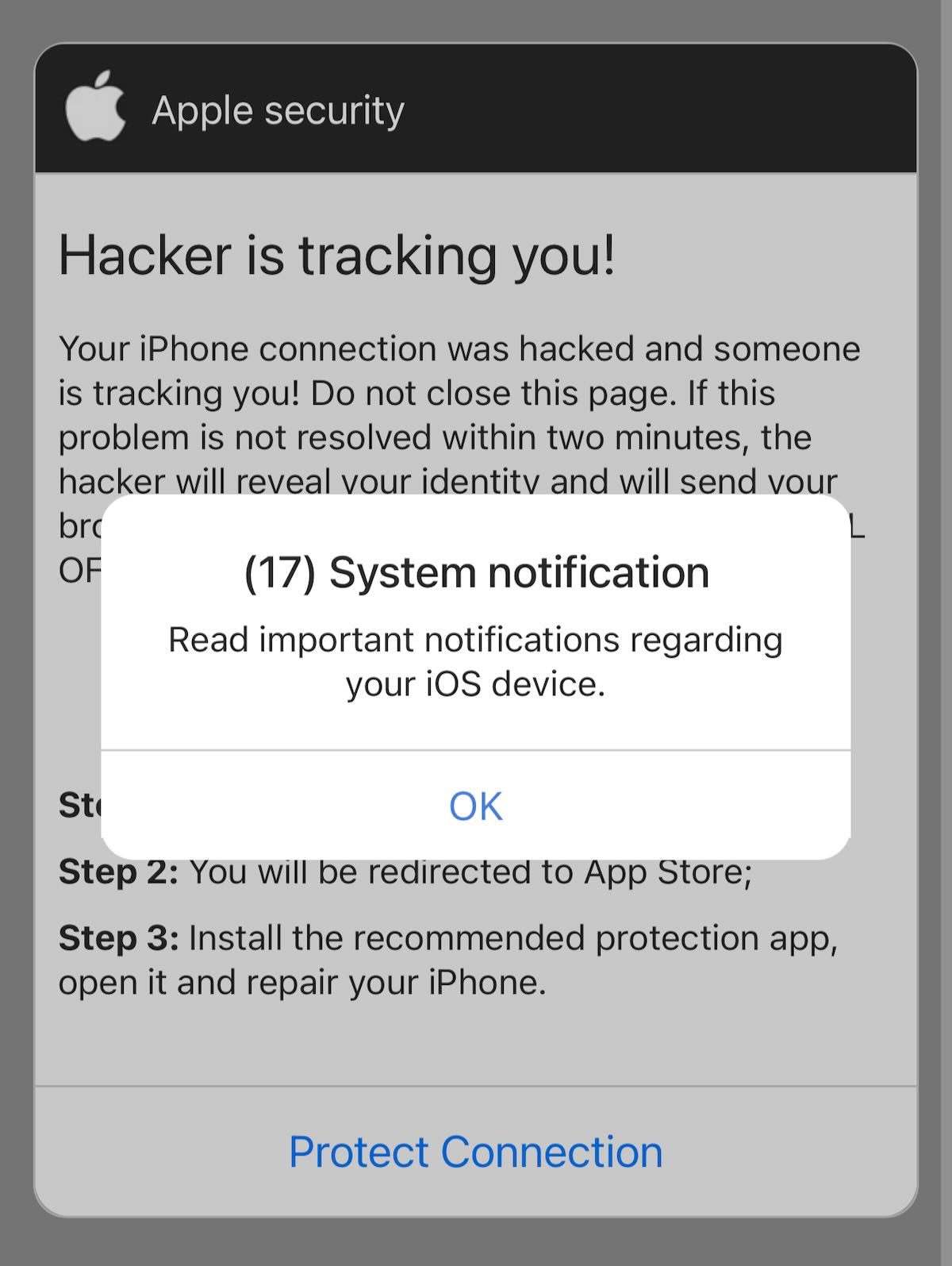
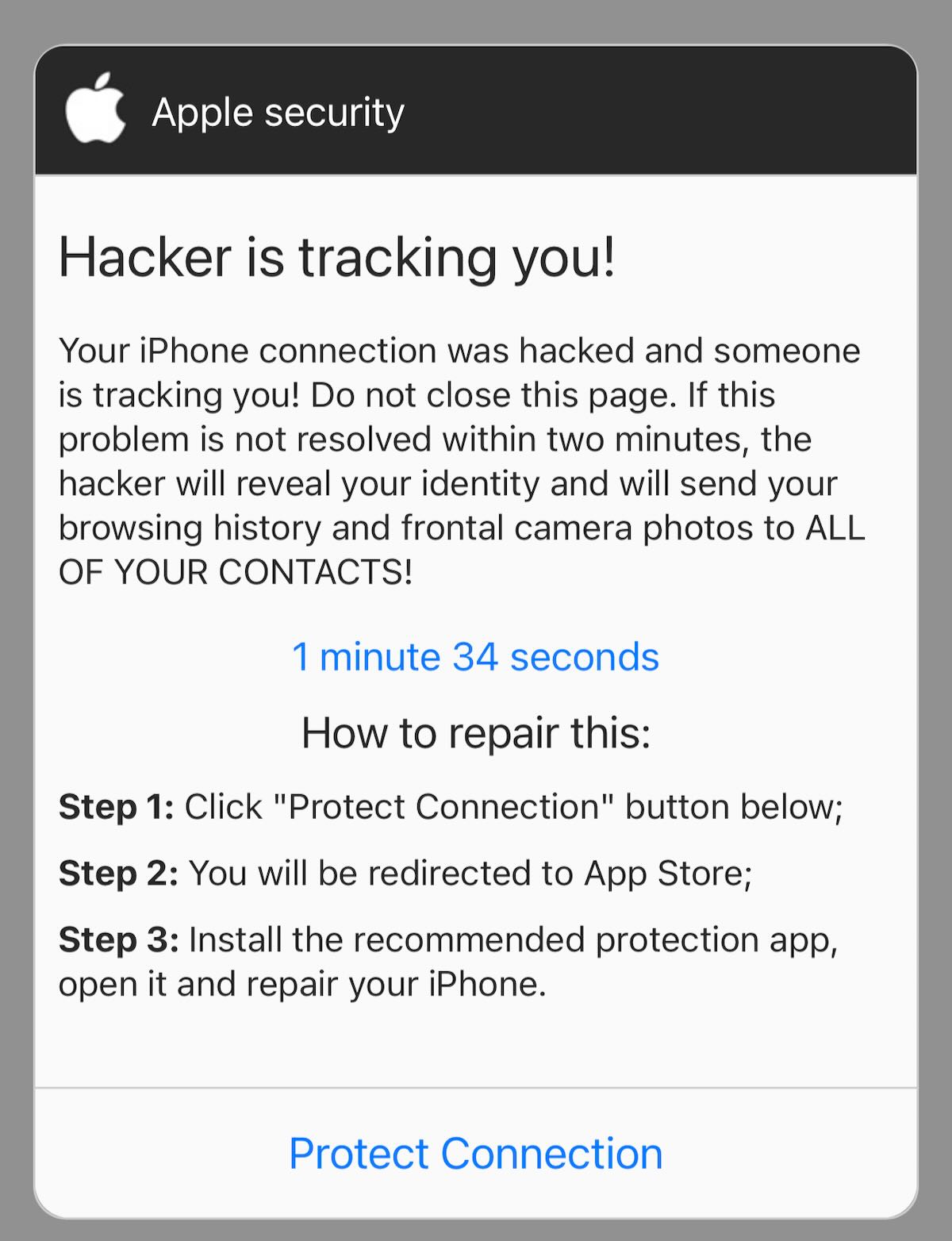
The message is always urgent — immediate action required.
The goal isn’t to inform — it’s to create stress, note how in the examples above there is even a countdown timer.
Legitimate companies do not contact you this way about infections or account problems. For example, Microsoft explicitly states that it does not initiate unsolicited support calls.
2. Moving You Off Safe Channels#
Next, you’re pushed toward the scammer’s communication path:
- Calling the number shown on screen
- Clicking a support link
- Replying to a message
This step matters — it removes you from official support channels.
Modern variants even manipulate search results or advertising placements so fake support numbers appear legitimate, a trend documented in security reporting such as coverage from TechRadar.
3. Taking Control#
Once engaged, the scammer typically asks you to install remote access software.
Commonly they will direct you to download programs such as:
- TeamViewer
- AnyDesk
- UltraViewer
- Microsoft Quick Assistant
These are legitimate remote support programs being used for malicious purposes.
They may:
- Show routine system logs as “evidence”
- Often times the scammer will have you open the operating system’s log files which has millions of entries into it including insignificant unnoticeable errors. The screens are highly technical and can confuse the average user. The scammer takes advantage of this and will tell you that every single log entry, even those which are normally there (such as computer power on / off) are viruses or hackers currently in your system. This is a tactic to instill a sense of urgency.
- Claim their intent is to remove threats
- Adjust system settings
- Watch you log into accounts
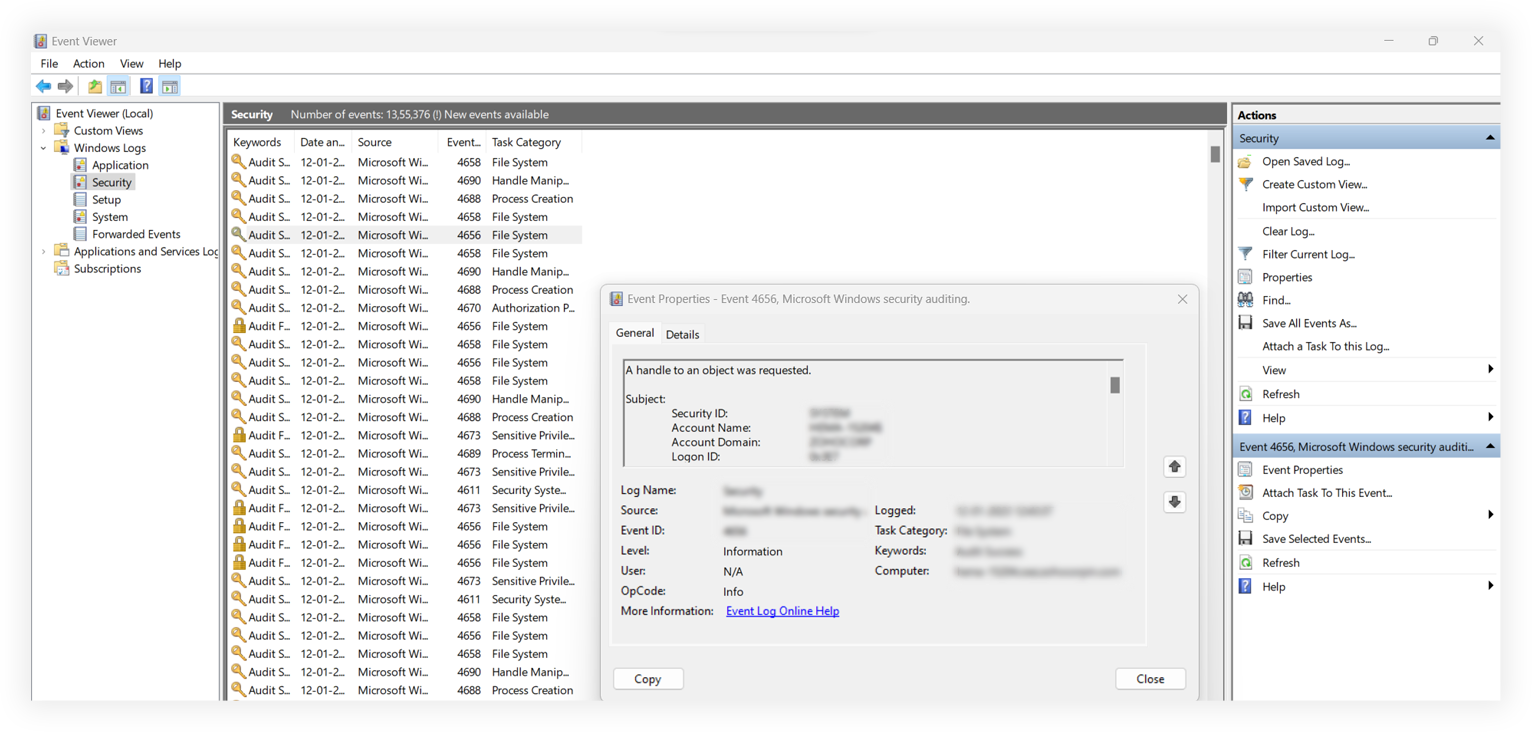
The FBI warns that granting remote access can expose files, credentials, and financial activity.
This is where the real damage happens.
4. Extracting Payment#
The story then shifts toward money.
Common narratives include:
- Charging for fake repair work
- Processing a “refund” requiring account access
- Moving funds to a “safe account”
- Requesting gift cards, wire transfers, or crypto
The scammer will often direct you to go to a bitcoin atm, the bank, bulk store, etc to purchase these items or to obtain money / crypto currency such as bitcoin. They will often want you to wire or even mail these gift cards etc to them. It will be a very strange means of paying someone. No professional would make these requests.
The FTC documents refund-style scams specifically designed to manipulate victims during this phase. I will be writing specifically about Refund Scams in the future.
These payment methods are chosen because they are difficult to reverse.
What These Scams Look Like in Practice#
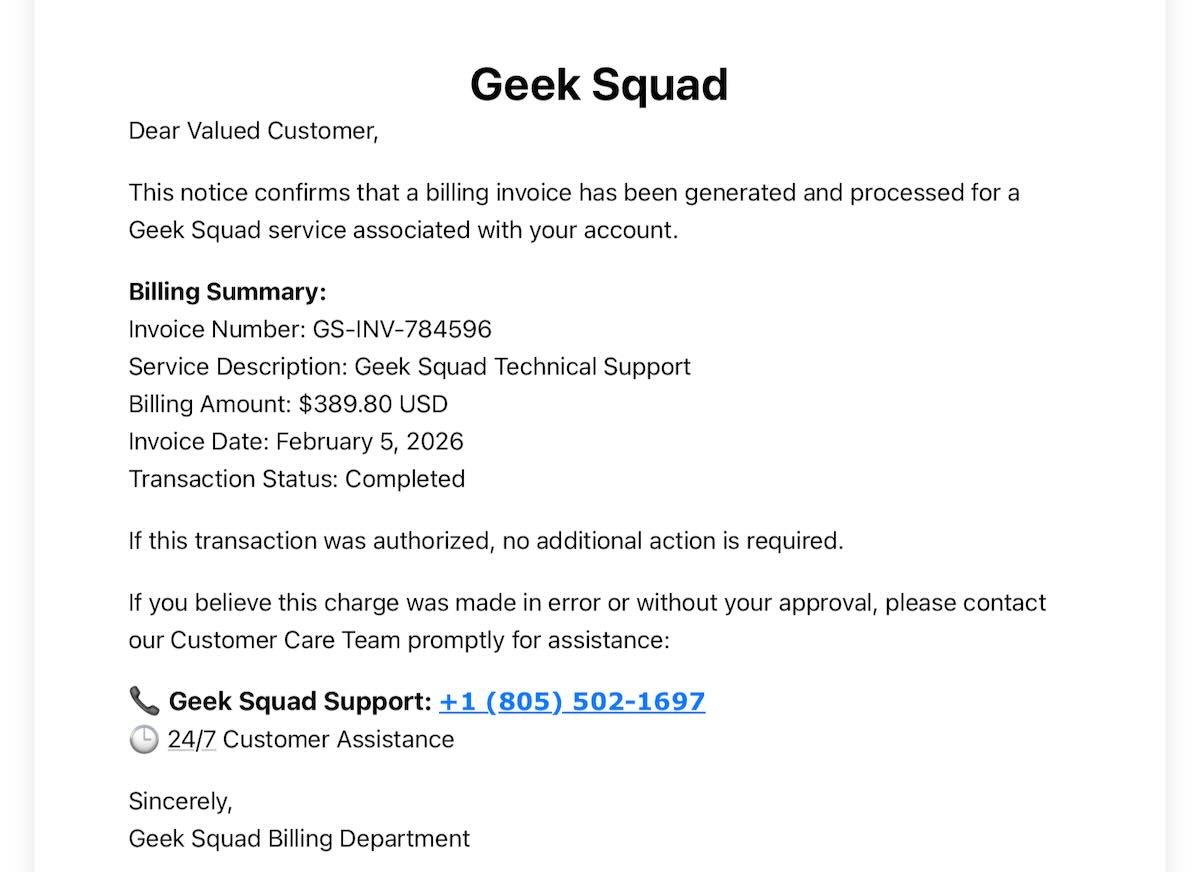
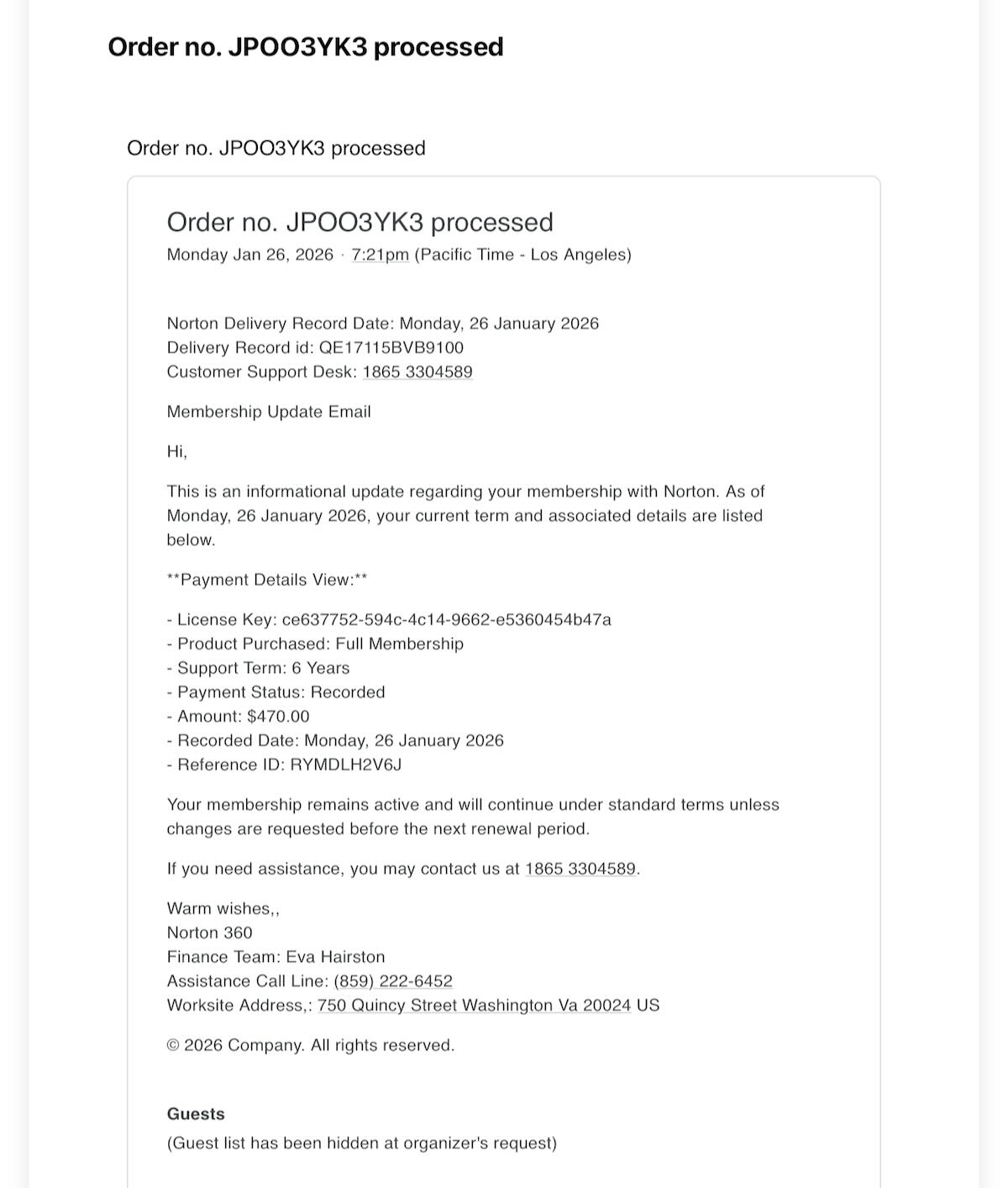
Typical appearances include:
- Locked browser warnings claiming infection
- Cold calls from “support departments”
- Scammers commonly impersonate companies like Microsoft, Norton, and McAfee
- Emails claiming that a refund is due to be paid to you or:
- Emails claiming that you payed for something such as Norton Anti-Virus
- Fake support replies on forums or social media
Consumer protection groups like AARP note that scammers frequently monitor forums and comment threads to post fake support contact information.
One useful rule:
If you didn’t initiate the support interaction, treat it as suspicious.
Simple Ways to Avoid Getting Pulled In#
You don’t need advanced security tools to avoid most of these.
- Never grant remote access to unsolicited contacts
- Ignore phone numbers shown in pop-ups
- Contact companies using official websites only
- Close suspicious browser tabs using task manager / force quit
- Maintain unique passwords and multi-factor authentication
These baseline practices align with recommendations from both the FTC and the FBI.
If You’ve Already Engaged#
Don’t panic — act methodically:
- Disconnect from the internet
- Remove remote software installed
- Change passwords (start with email accounts)
- Contact financial institutions
- Report the incident
Reporting resources:
Quick response dramatically limits damage.
Perspective#
Tech support scams succeed because they target human reaction, not technical weakness.
They exploit urgency, authority signals, and confusion — things every person is susceptible to under the right conditions.
The strongest defense isn’t software.
It’s process discipline.
Slow down. Verify independently. Initiate support yourself. If you suspect that you are in a situation where you are being taken advantage of you are welcome to call Joe and Kayla.
That alone stops most of these attacks before they begin.
