Today we’re going to discuss a news clip from ABC 10 concerning the theft of nearly $700,000.
This news clip was recently shared in a local community group, the sharer’s message: don’t allow anyone to access your computer. While rudimentarily correct at a basic level, today’s cybersecurity is more complex. Let’s discuss how allowing a trusted service provider, such as ourselves and our tools, access can prevent such a tragedy from occurring.
Let’s break down the process from initiation to eventual theft.
Initial Email #
The couple in the video received an email informing them that they had made a significant purchase on Amazon. They were conveniently provided a number to call to modify or cancel the order. Since they had not placed the order this instilled a sense of urgency to action. Such urgency is a common tool of scammers.
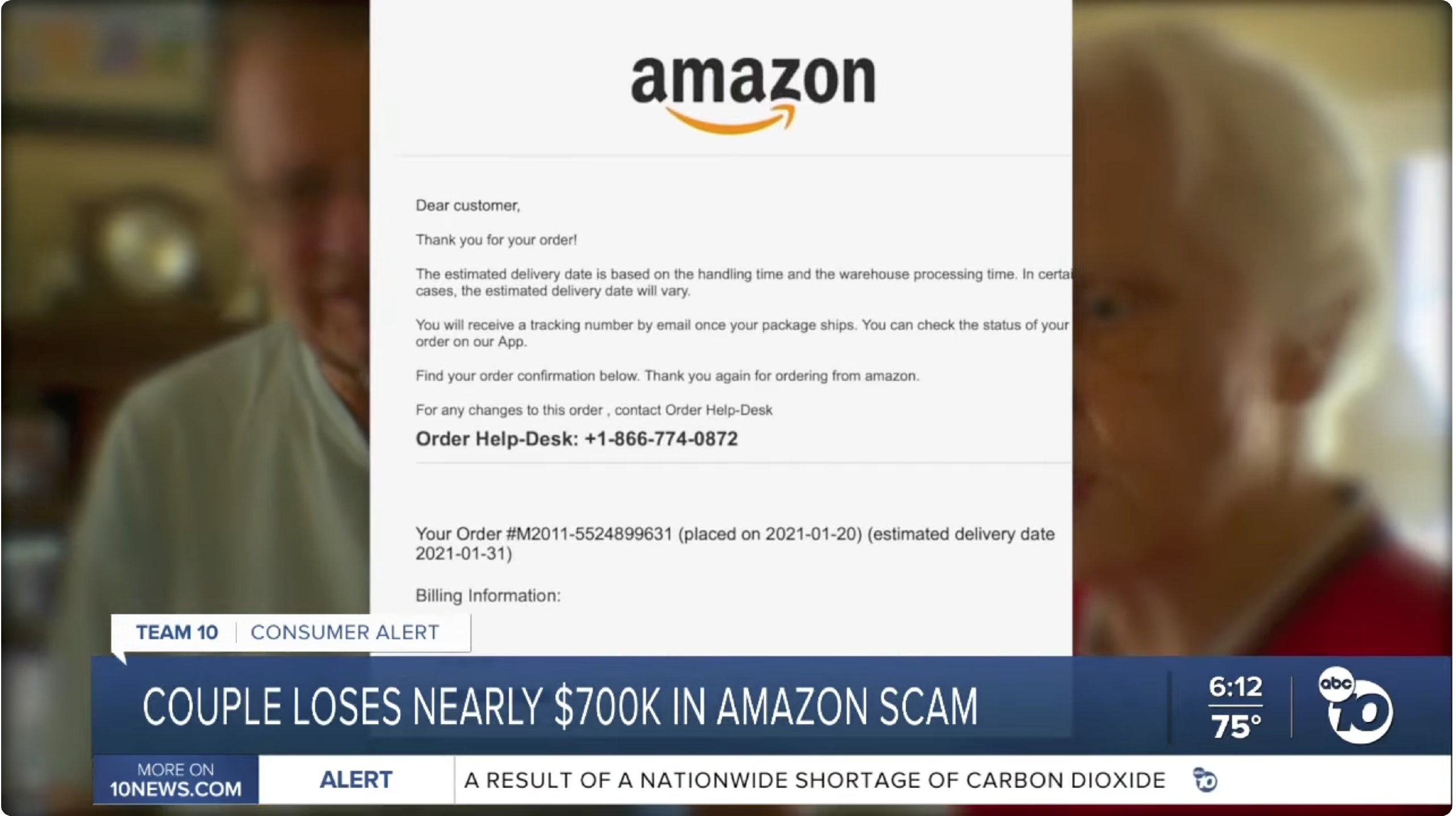
Fueled by this urgency the couple called the phone number in the email. The email was part a “phishing” campaign. This was the second mistake, did you catch the first?
Intervention: Security Awareness
Managing the Human Element
A component of our Managed Service Plans includes access to Security Awareness Training (or SAT). The awareness of our customers is the #1 defense against refund, tech-support, and other scams. We can manage your computer, install anti-virus, and actively monitor for threats. However, we cannot stop you from going to the bank and withdrawing money to send. This is where your knowledge of phishing, scams, and similar attacks protects you.
Our educational component of service will better protect you through awareness than any software we can provide at this phase of the scam.
The first mistake which the couple made was not simply deleting a phishing / scam email, the second was calling the number in the email.
Safe Steps: #
- Log into Amazon via your established methods, if you are an Amazon customer you know how to do this already. Access the site via the web browser or app as you normally would.
- Check for recent order activities. This will instantly rule out that an order was made on your account.
- To be doubly secure, check your bank / credit card which would be billed for sales through Amazon. Look at recent transactions.
The above actions would have indicated that this was a false transaction and email.
Remote Desktop Connections #
The couple called the phone number which was in the email. This put them squarely in the control of the scammer. The scammer then proceeded to tell them all of their worst fears were true. They said things like this was a “real order”, it was “billed to their card”, and Amazon needed “their help” to refund them.
The scammer then initiated a remote desktop session to interact with the victims.
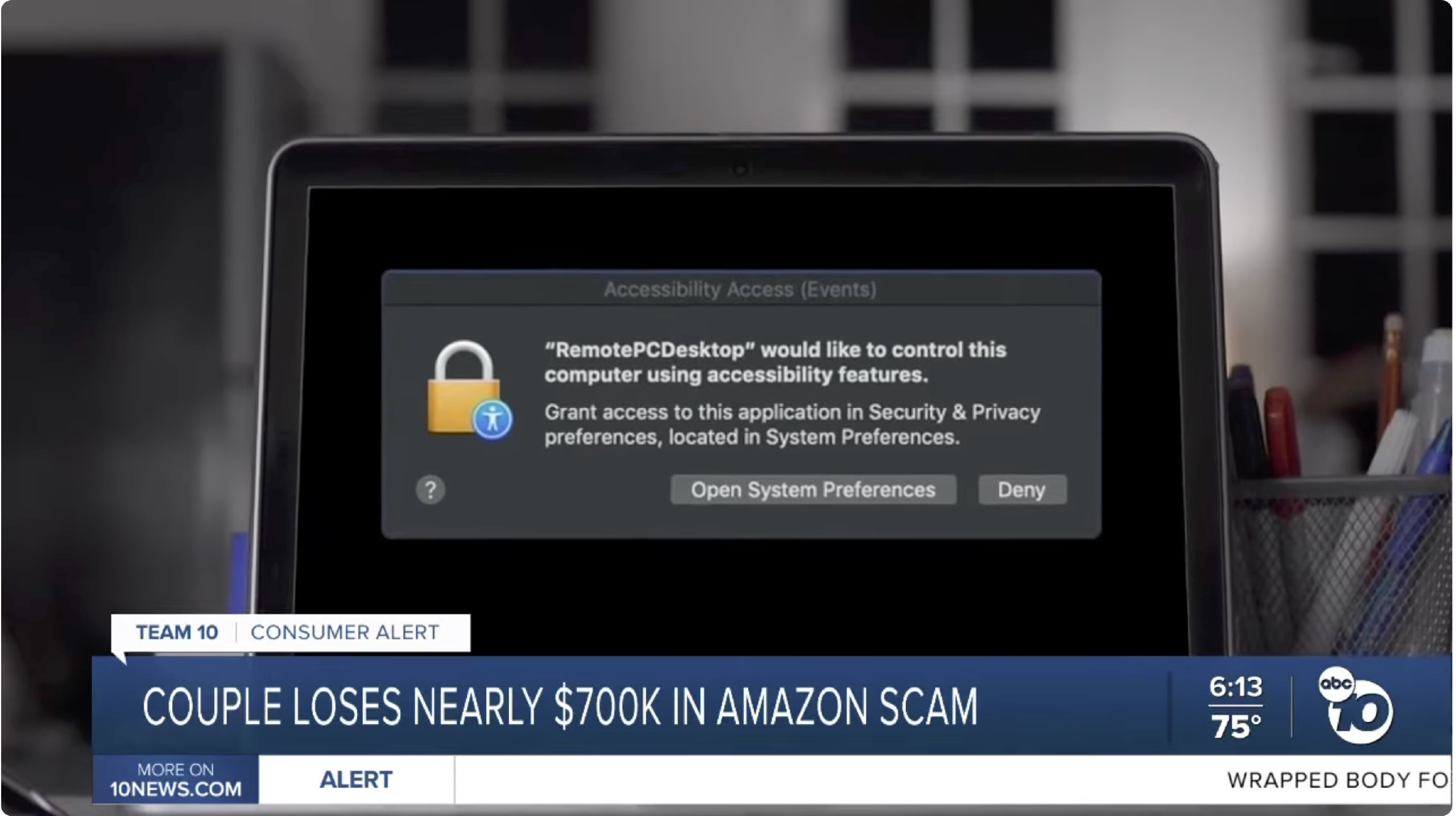
There is never a situation that any company would need to connect to your computer to refund you.
Intervention: Active Monitoring
Rogue / malicious screen connects can be detected
This is the second layer of our protection. #
Level 1: Rogue Screen Connect Alerts.
The presence of an unauthorized remote desktop program (screen connect) will likely trigger an alert within our monitoring program. If we are providing you remote monitoring and management services by our service contract we are the only people who have any business to connect to your computer in this manner. You or trusted individuals can be granted permission to use our system to remote into your computer if needed. Our system will monitor for the presence of these programs and alert our technicians to this potential intrusion. You will likely be getting a phone call, the remote access program will likely be stopped remotely.
Level 2: Active Threat Monitoring.
The installation of an unauthorized remote desktop application, or website visit will signal our threat-hunting software that a problem may be occurring. This singular action itself will not trigger action. This signal will be aggravated with others which may eventually trigger an alert.
Clean Up
Our monitoring system logs all installed software. In the event of intrusion this will assist in cleaning up the computer to get it back to the pre-intrusion state.
Safe Steps: #
- Deny any attempt for someone to connect to your computer
- Immediately call your trusted technical service provider
- Do not answer your phone when calls come from unknown numbers, the scammers use fear, anxiety, and pressure to convince you to send them money. Once they have your number they will become persistent.
Fake Amazon Website #

Once connected the scammers directed the victims to a website to “prove” that a transaction had occurred. Such fake sites will steal your login credentials and provide you with false information. The scammers also took them to another website, or the victims’ computer’s command line interface (Terminal on Mac / Linux / Unix) to “process the refund”. This is a common tactic used by scammers.
When the victim typed in $2000, the scammer then typed in an additional three zeros to make the “total amount refunded” appear to be $200,000. Again, this is a common tactic used to convince you that you have “just inadvertently stolen” from Amazon. The scammer becomes hostile, now they want “their money back”. They will threaten you with police action, they will tell you that “you’re a good person let’s just settle this”, they will do whatever they think they need to so that you will comply.
They will attempt to isolate you with commands and suggestions that it is highly inappropriate, or that time does not exist for you to seek the advice of others. The pressure will be tremendous, and they are persistent. You will potentially be transferred to another “agent” (scammer) who is specialized in getting the money back.
Intervention: Web Filtering & Active Monitoring
Websites which meet malicious criteria are blocked
This is the third layer of protection #
Level 1: DNS Protection
Part of our Managed Services Plan is web filtering. This is performed by software which is installed into your computer which runs silently in the background. It does a few things to protect you and your privacy like blocking ads and tracking. However, its true purpose is blocking malicious websites which intend to steal your data, scam you, inject viruses, or do other harm. This process is called DNS filtering. When scammers make fake Amazon, bank, or other phishing websites they are quickly detected and added to a list of known malicious sites. Because of this, scammers are constantly registering new websites in the hopes of getting a few days to a week of use out of them before they become known. Our DNS filtering software blocks known, and newly registered websites from loading on your computer.
- You will likely get a message from FroJoe that the site you are attempting to visit has been blocked
- You can contact us by an icon in your system tray (next to the time display in the corner on your computer) for advice
This is the fourth layer of protection #
Level 2: Active Threat Monitoring
When the scammer directs you to malicious sites, even if they are not caught by the web filtering, the threat monitoring software knows. It is calculating the recent screen connect, the malicious website traffic, the textual exchanges occurring for the “refund process” where the additional 0’s were added, it may weigh the content of the initial email you received. In many such cases it will automatically trigger an alert and an investigation. The incident is immediately sent to our partner’s 24/7/365 Security Operations Center (SOC) where some of the best cybersecurity experts will alert us, provide remediation advice, and if necessary take the computer offline entirely to stop the threat. You will get a phone call from us, if the computer is taken offline a message will appear on your screen that your machine is now isolated completely from the internet. While this may be an extreme example, this is an important part of preventing hackers from getting access to anything else on your computer, or other computers on the same network.
There are documented cases of where scams have been successfully stopped by active monitoring. The victim under the influence of the scammer often will fight against the efforts of their trusted service provider, almost as if they have been brainwashed for that short period of time.
Safe Steps #
- If you get this deep into the scammer’s net, then you are completely under the influence of the scammer’s spell
- Always ask yourself “does this seem normal or professional, is there a safer way to do this?”
- Contact someone you trust like your banker, law enforcement, or family member to help you make a safe decision
- No company particularly one as established as Amazon, will “accidentally allow” you to refund yourself $198,000, ask yourself “does this make sense?”
- Contact FroJoe for assistance
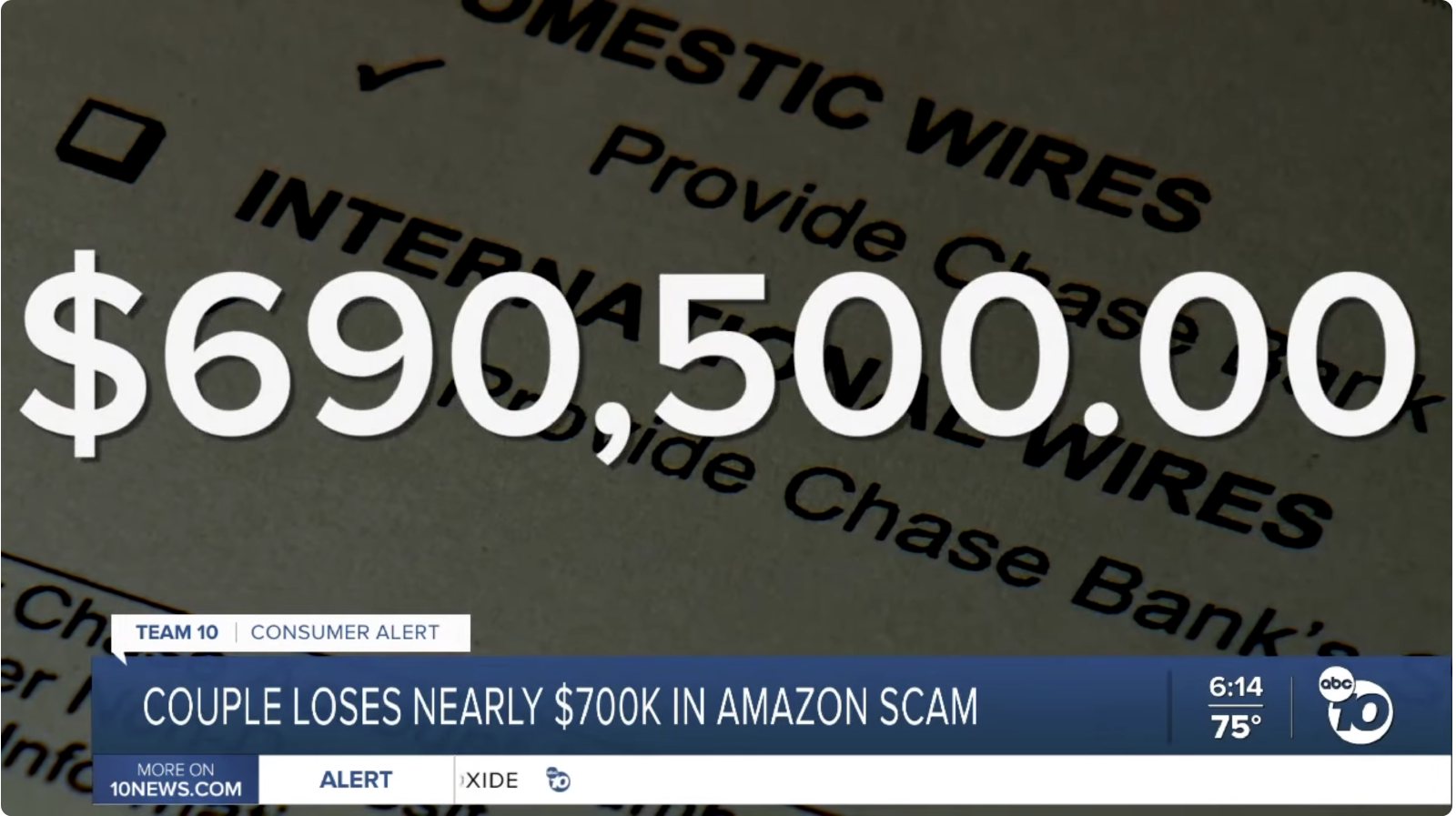
Bank Wire Transfers #
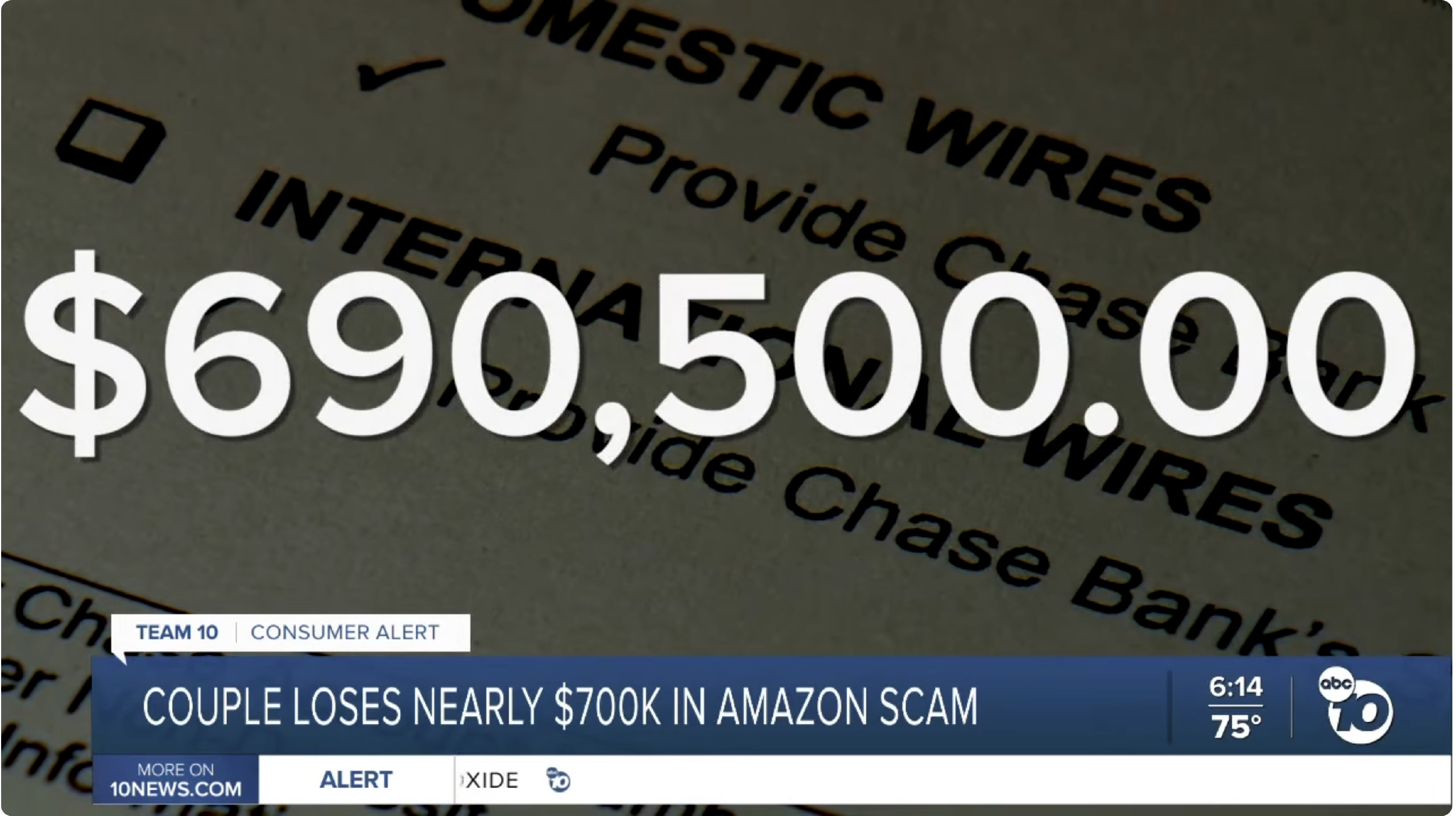
By this point the scammer has gotten complete control of the situation. The victims in the video lacked the security as described above, thus they missed out on the interventions which would have helped stop this tragedy. Unfortunately, if the scam gets to this point in the process no level of computer security would have stopped what happens next.
Somehow the scam grows to nearly $700,000 in theft with no means of recovery as the victim themselves were the primary actors in the theft.
Tragedy #
How do you recover? How can you recover? The answers to these questions are outside our scope of practice. You can inquire with your bank, your insurance company, but you will face significant challenges. Our job as your trusted support company is to provide you with the training, software, and tools to prevent such events from happening. While our services normally prevent such tragedies from happening, there is always a risk involved in using the internet.
You can watch the full video below, you may have to click through to YouTube directly.
Multiple Layers of Security
Four Layers of protection #
As you have seen above we have talked about four separate layers of protection that we can provide you to prevent you from becoming the victim of a scam like this. Currently (March 2026) home users can access this protection for $35 a month per computer, or $60 for two within the same home (residential plans).
Can You Spot Potential Intervention? #
Now that we have discussed how our Managed Services Plans can intervene, can you spot where FroJoe would have stopped this scam?
Video Below You may need to click to watch on YouTube directly
How can we help you today? #
Images and content are used under Fair Use provisions as we are reporting in a news format
