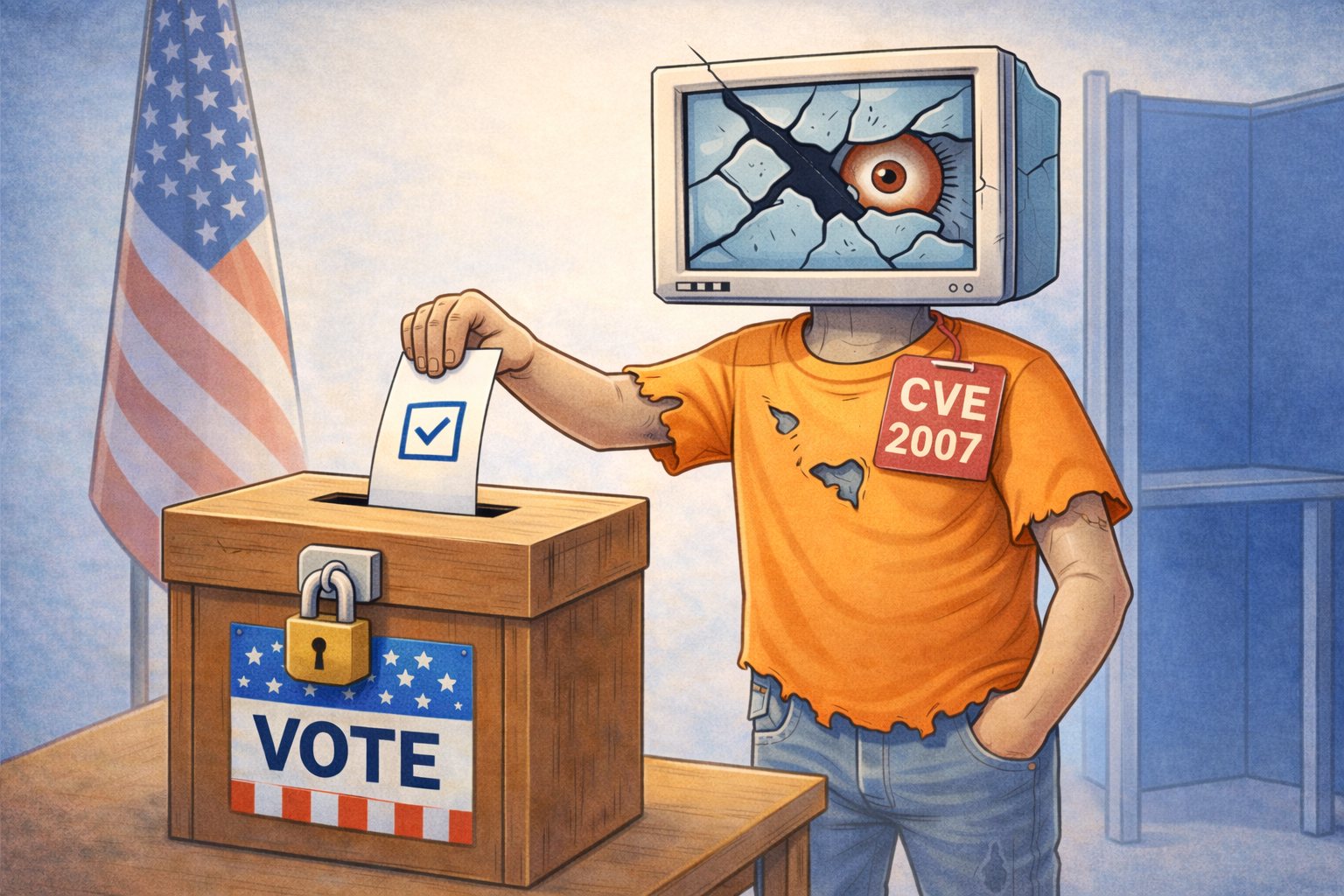
Vulnerabilities old enough to vote… #
Many cyber incidents do not begin with sophisticated hacking techniques. Instead, they often start with something much simpler: software that has not been updated. When operating systems, browsers, and applications fall behind on security patches, attackers can use publicly known vulnerabilities to gain access to a computer or network.
As the number of disclosed vulnerabilities continues to grow each year, keeping systems updated has become one of the most important parts of cybersecurity. Regular patching, combined with monitoring for unusual behavior, helps reduce the chances that a known weakness can be used to compromise a system. According to Cisco Talos vulnerabilities from 2007, which would be old enough to vote in many countries, were actively causing problems.
Why Software Updates Matter #
Software updates are one of the most important but often overlooked parts of cybersecurity. Every major operating system and application contains millions of lines of code, and over time researchers inevitably discover flaws that could potentially be abused by attackers. When these flaws are identified, vendors release patches to correct the problem before it can be widely exploited.
Installing these updates closes security gaps that might otherwise remain open. Without the update, the vulnerability continues to exist exactly as originally discovered. Attackers often monitor these disclosures closely because once a vulnerability becomes public, it can provide a clear roadmap for how to compromise unpatched systems.
Vulnerabilities Are Increasing Every Year #
The number of publicly disclosed vulnerabilities continues to rise each year. In 2025 alone, nearly 48,200 vulnerabilities were recorded in the CVE database, averaging more than 130 new disclosures every day. Each of these represents a weakness that could potentially be used to bypass security controls, run malicious code, or gain unauthorized access.
This growing volume makes it difficult for individuals and small organizations to keep track of every update manually. Each application, operating system, and network device may release its own security advisories and patches. Without a consistent patching process, important updates can easily be missed.
Many Attacks Use Old Vulnerabilities #
One surprising aspect of cybersecurity is that attackers frequently rely on vulnerabilities that have been known for years. Security research has shown that many actively exploited vulnerabilities originate from older software flaws that remain unpatched in real environments. In some cases, vulnerabilities disclosed more than a decade ago are still being used successfully.
This happens because outdated systems are common in both homes and businesses. Devices may continue running older software simply because they appear to be functioning normally. Unfortunately, attackers often prefer these older weaknesses because the technical details for exploiting them are widely documented.
Everyday Applications Are Common Targets #
Operating systems are not the only software that requires regular updates. Many vulnerabilities are discovered in everyday applications such as web browsers, document viewers, office software, and communication tools. These programs interact with external data frequently, which increases the opportunity for malicious files or websites to exploit weaknesses.
For example, a malicious website may attempt to exploit a vulnerability in a web browser, or a specially crafted document could attempt to take advantage of a flaw in a document viewer. When the affected software is fully patched, the exploit typically fails. When it is outdated, the vulnerability may still be accessible.
Attackers Often Move Faster Than Users #
Attackers frequently move quickly after vulnerabilities are disclosed. Once a security advisory becomes public, researchers and criminals alike can analyze the flaw and begin developing exploitation techniques. In some cases, proof-of-concept attack code appears within days of a vulnerability announcement.
This creates a race between patching and exploitation. Organizations that apply updates quickly reduce their exposure window. Systems that remain unpatched for weeks or months become increasingly attractive targets because attackers know the vulnerability is still present.
Patching Is One of the Most Effective Defenses #
Despite the growing sophistication of cyber threats, patching remains one of the most effective ways to reduce risk. Applying security updates removes many of the weaknesses attackers rely on to gain initial access. While no security measure is perfect, keeping systems updated eliminates a large percentage of opportunistic attacks.
Patching also helps protect against automated scanning tools that search the internet for vulnerable systems. These tools often look specifically for outdated software versions associated with known vulnerabilities. When systems are updated regularly, they become much harder targets for these automated attacks.
The Challenge for Small Businesses and Home Users #
Large organizations often maintain dedicated teams responsible for vulnerability management and patch deployment. Home users and small businesses rarely have that level of dedicated oversight. Updates may be postponed because systems appear to be working normally, or because users are unsure which updates are important.
Unfortunately, this creates a common security gap. When updates are delayed for long periods, systems gradually accumulate known vulnerabilities. Over time these weaknesses increase the chances that an automated attack or targeted exploit could succeed.
Monitoring Helps Catch Problems Early #
Even when systems are patched regularly, monitoring still plays an important role in cybersecurity. New vulnerabilities continue to emerge, and not every threat relies solely on software flaws. Monitoring tools watch for unusual activity that may indicate an attempted compromise.
Examples of suspicious activity can include unexpected programs launching, unusual network connections, or repeated login attempts. Identifying these signals early allows security teams to investigate and respond before a larger incident develops.
Our remote active monitoring and management service ensures that your computer stays updated and that vulnerabilities are identified and managed.
A Practical Approach to Staying Secure #
For most home users and small businesses, cybersecurity does not need to be complicated. Maintaining updated systems, enabling automatic updates where possible, and monitoring for unusual activity provide a strong foundation for protecting everyday technology. These steps reduce the likelihood that attackers can exploit known weaknesses.
Security is most effective when it is proactive rather than reactive. By keeping software updated and watching for early warning signs, many common threats can be prevented before they cause disruption.
How FroJoe Helps #
At FroJoe Tech Services, the goal is to reduce risk before problems occur. This includes tracking security updates, applying patches when vulnerabilities are disclosed, and monitoring systems for signs of suspicious activity. By addressing both known vulnerabilities and unusual behavior, this approach helps close common attack paths.
For home users and small businesses who do not have time to track every security advisory, managed support provides a practical way to keep systems maintained and monitored. The result is technology that stays secure and reliable without requiring constant attention from the user.
Want Help Protecting Your Computer? #
If you’d like help protecting your computers from exploited vulnerabilities, FroJoe Tech Services provides proactive monitoring, security hardening, and remote technical support for home users and small businesses.
Reach out anytime if you’d like to talk about improving your computer security and preventing problems before they happen.
How can we help you today? #
Sources #
Cisco Talos Intelligence. Patch, Track, Repeat: The 2025 CVE Retrospective
https://blog.talosintelligence.com/patch-track-repeat-2025-cve-retrospective/
MITRE. Common Vulnerabilities and Exposures (CVE) Program
https://www.cve.org/
Microsoft Threat Intelligence. AI as tradecraft: How threat actors operationalize AI
https://www.microsoft.com/security/blog/
